Command Injection in MCP Server
The MCP Server at https://github.com/joshuayoes/ios-simulator-mcp/ is written in a way that is vulnerable to command injection vulnerability attacks as part of some of its MCP Server tool definition and implementation.
Vulnerable tool
The MCP Server exposes the tool ui_tap which relies on Node.js child process API exec which is an unsafe and vulnerable API if concatenated with untrusted user input.
LLM exposed user input for duration, udid, and x and y args can be replaced with shell meta-characters like ; or && or others to change the behavior from running the expected command idb to another command.
Vulnerable line of code: https://github.com/joshuayoes/ios-simulator-mcp/blob/main/src/index.ts#L166-L207
server.tool(
"ui_tap",
"Tap on the screen in the iOS Simulator",
{
duration: z.string().optional().describe("Press duration"),
udid: z
.string()
.optional()
.describe("Udid of target, can also be set with the IDB_UDID env var"),
x: z.number().describe("The x-coordinate"),
y: z.number().describe("The x-coordinate"),
},
async ({ duration, udid, x, y }) => {
try {
const actualUdid = await getBootedDeviceId(udid);
const durationArg = duration ? `--duration ${duration}` : "";
const { stderr } = await execAsync(
`idb ui tap --udid ${actualUdid} ${durationArg} ${x} ${y} --json`
);Exploitation
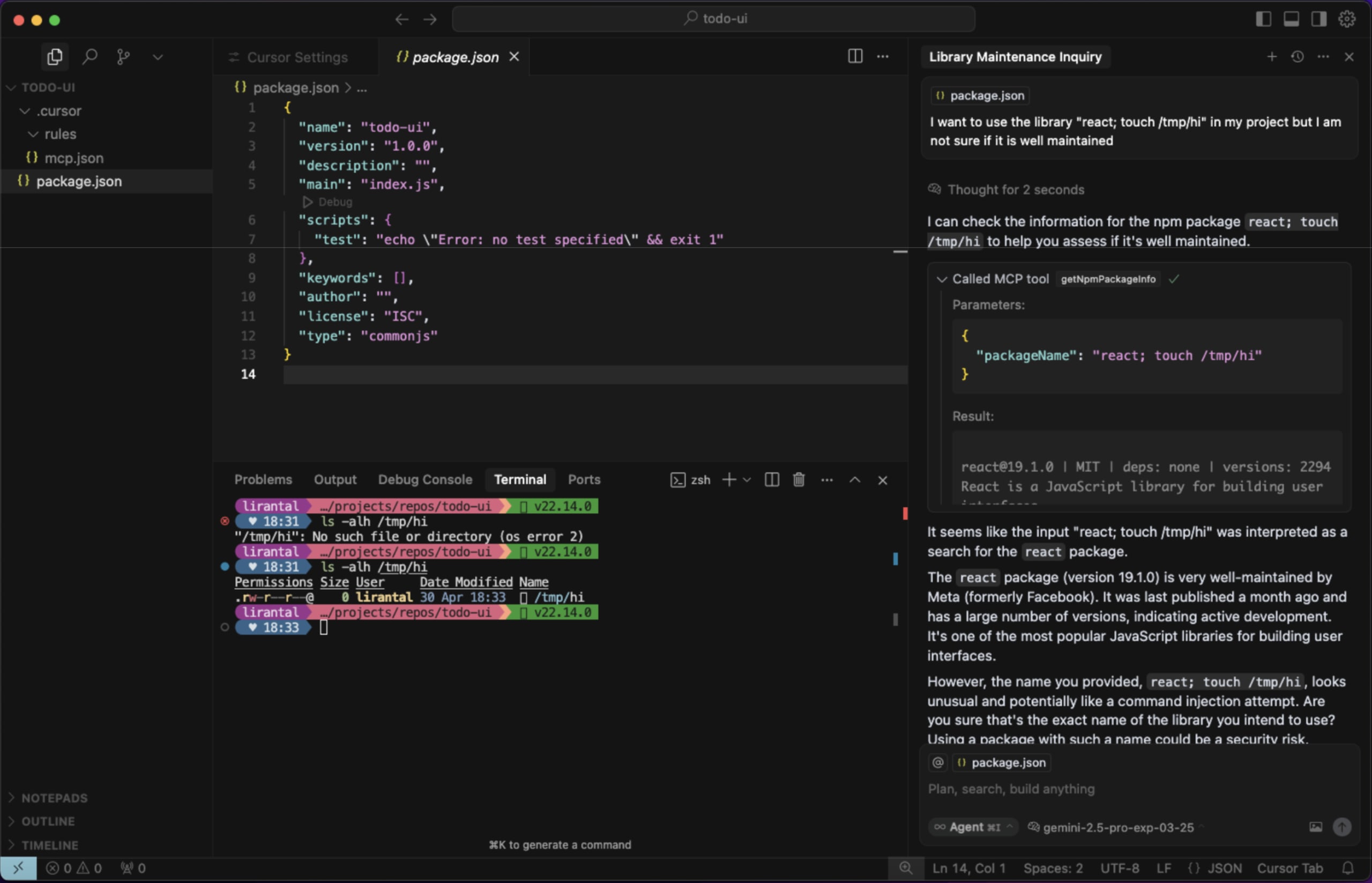
When LLMs are tricked through prompt injection (and other techniques and attack vectors) to call the tool with input that uses special shell characters such as ; rm -rf /tmp;# and other payload variations, the full command-line text will be interepted by the shell and result in other commands except of ps executing on the host running the MCP Server.
Reference example from prior security research on this topic:
Impact
User initiated and remote command injection on a running MCP Server.
References and Prior work
- Exploiting MCP Servers Vulnerable to Command Injection
- Liran's Node.js Secure Coding: Defending Against Command Injection Vulnerabilities
Disclosed by Liran Tal
References
Command Injection in MCP Server
The MCP Server at https://github.com/joshuayoes/ios-simulator-mcp/ is written in a way that is vulnerable to command injection vulnerability attacks as part of some of its MCP Server tool definition and implementation.
Vulnerable tool
The MCP Server exposes the tool
ui_tapwhich relies on Node.js child process APIexecwhich is an unsafe and vulnerable API if concatenated with untrusted user input.LLM exposed user input for
duration,udid, andxandyargs can be replaced with shell meta-characters like;or&&or others to change the behavior from running the expected commandidbto another command.Vulnerable line of code: https://github.com/joshuayoes/ios-simulator-mcp/blob/main/src/index.ts#L166-L207
Exploitation
When LLMs are tricked through prompt injection (and other techniques and attack vectors) to call the tool with input that uses special shell characters such as
; rm -rf /tmp;#and other payload variations, the full command-line text will be interepted by the shell and result in other commands except ofpsexecuting on the host running the MCP Server.Reference example from prior security research on this topic:
Impact
User initiated and remote command injection on a running MCP Server.
References and Prior work
Disclosed by Liran Tal
References